| Table of Contents |
|---|
...
- Open AWS Console, go to IAM under the services tab
- Policy Creation:
- Go to Policies > Create Policy
- Go to the JSON tab
Copy the below policy document:
Info icon false {
"Version": "2012-10-17",
"Statement": [
{
"Action": [
"kinesis:GetShardIterator",
"kinesis:GetRecords",
"kinesis:DescribeStream",
"kinesis:ListTagsForStream"
],
"Resource": [
"AgentEventsKinesisARN","CTRKinesisARN"
],
"Effect": "Allow",
"Sid": "AllowReadKinesis1"
},
{
"Action": "kinesis:DescribeLimits",
"Resource": "*",
"Effect": "Allow",
"Sid": "AllowReadKinesis2"
},
{
"Action": [
"connect:Get*",
"connect:Describe*",
"connect:List*"
],
"Resource": [
"AmazonConnectInstanceARN","AmazonConnectInstanceARN/*"
],
"Effect": "Allow",
"Sid": "AllowReadAmazonConnect1"
},
{
"Sid": "AllowReadAmazonConnect2",
"Effect": "Allow",
"Action": "ds:DescribeDirectories",
"Resource": "*"
},
{
"Action": "connect:GetFederationTokens",
"Resource": "*",
"Effect": "Deny",
"Sid": "DenyFederationTokens"
}
]
}- Replace AgentEventsKinesisARN with the ARN of the Agent Events Kinesis Stream created in the previous section
- To view the ARN, open a new console window and go to Kinesis > select the stream under Kinesis data streams (connect-agentevents in this example)
- On the Details tab, copy the Stream ARN
- To view the ARN, open a new console window and go to Kinesis > select the stream under Kinesis data streams (connect-agentevents in this example)
- Replace CTRKinesisARN with the ARN of the CTR Kinesis Stream created in the previous section
- To view the ARN, open a new console window and go to Kinesis > select the stream under Kinesis data streams (connect-ctr in this example)
- On the Details tab, copy the Stream ARN
- To view the ARN, open a new console window and go to Kinesis > select the stream under Kinesis data streams (connect-ctr in this example)
- Replace AmazonConnectInstanceARN with ARN of the Amazon Connect instance
- To view the ARN, open a new console window and go to Amazon Connnect > select your Amazon Connect instance
- On the overview tab, copy the Instance ARN
- To view the ARN, open a new console window and go to Amazon Connnect > select your Amazon Connect instance
- Click Review Policy
- Policy Name: emite-role-policy
- Click Create Policy
...
- Policy Creation:
- Go to Policies > Create Policy
- Go to the JSON tab
Copy the below policy document:
Info icon false {
"Version": "2012-10-17",
"Statement": [
{
"Action": [
"s3:Get*GetObject",
"s3:List*ListBucket"
],
"Resource": [
"ConnectS3BucketARN",
"ConnectS3BucketARN/Analysis/Voice/*"
],
"Effect": "Allow",
"Sid": "AllowGetContactLensData"
},
{
"Action": [
"kms:DescribeKey",
"kms:GenerateDataKey",
"kms:Decrypt"
],
"Resource": [
"ConnectS3BucketKmsArn"
],
"Effect": "Allow",
"Sid": "AllowDecryptContactLensData"
}
]
}- Replace ConnectS3BucketARN with the ARN of the Bucket used to store Contact Lens data
- Open a new console window and go to Amazon Connnect > select your Amazon Connect instance
- Go to Data Storage > Edit Call Recordings
- You should see the S3 bucket name:
- Open a new console window and go to S3
- Search and open the bucket name in the previous step
- Go to properties tab, copy the Bucket ARN
- Open a new console window and go to Amazon Connnect > select your Amazon Connect instance
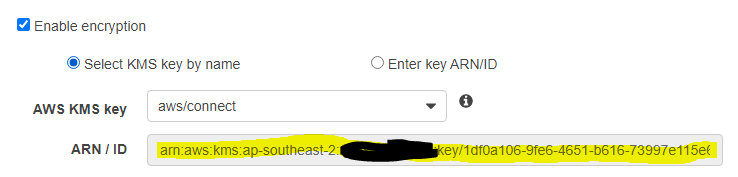
- Replace ConnectS3BucketKmsArn with the ARN of the S3 Encryption key used for Contact Lens Data
- Open a new console window and go to Amazon Connnect > select your Amazon Connect instance
- Go to Data Storage > Edit Call Recordings
- Copy the ARN of the Encryption Key
- Open a new console window and go to Amazon Connnect > select your Amazon Connect instance
- Click Review Policy
- Policy Name: emite-role-policy-contactlens
- Click Create Policy
...
- eMite EC2 details (only if server will be deployed on your AWS account)
- eMite EC2 external IP
- RDP credentials
- EmiteRole ARN
- Go to IAM Roles
- Click the emite-role role
- Copy the Role ARN
- Go to IAM Roles
- Amazon Connect Instance ARN
- Go to Amazon Connnect > select your Amazon Connect instance
- On the overview tab, copy the Instance ARN
- AgentEvents Kinesis Stream ARN
- To view the ARN, open a new console window and go to Kinesis > select the stream under Kinesis data streams (connect-agentevents in this example)
- On the Details tab, copy the Stream ARN
- CTR Kinesis Stream ARN
- To view the ARN, open a new console window and go to Kinesis > select the stream under Kinesis data streams (connect-ctr in this example)
- On the Details tab, copy the Stream ARN
- Elasticsearch Endpoint URL
- Go to Elasticsearch > emite-kinesis-connect domain
- Copy the Endpoint
- Preferred Time Zone
- Please send us your preferred timezone in IANA format
- Common Timezones
- Australia/Sydney
- Europe/Dublin
- Europe/Berlin
- Asia/Tokyo
- America/New_York
- America/Los_Angeles
- Additional Timezones can be found here:
...